Introduction
If you intend (or already are) providing a “Professionally Maintained Public Wireless LAN Access Point” in Switzerland, you are affected of the new article (Art. 19 Abs. 2 VÜPF) that became effective on March 1st 2018:
Original: Art. 19 Abs. 2 VÜPF: ‘Die FDA haben bei professionell betriebenen öffentlichen WLAN-Zugangspunkten sicherzustellen, dass alle Endbenutzerinnen und -benutzer mit geeigneten Mitteln identifiziert werden.’
Translated: ‘Telecommunications Service Providers are obligated to identify end users in ‘Professionally Maintained Public Wireless LAN Access Points’ with ‘suitable methods”.
Because this article leaves room for interpretation, a leaflet got published to clarify the four decisive matters of this article:
– What is an “Wireless LAN Access Point”?
– When is a Wireless LAN “public”?
– What defines “professionally maintained”?
– What are “suitable methods” of identification?
This leaflet is in German, so I decided to try my best and translate it into English, to give you a little heads up about the situation here in Switzerland.
What is a “Wireless LAN Access Point”?
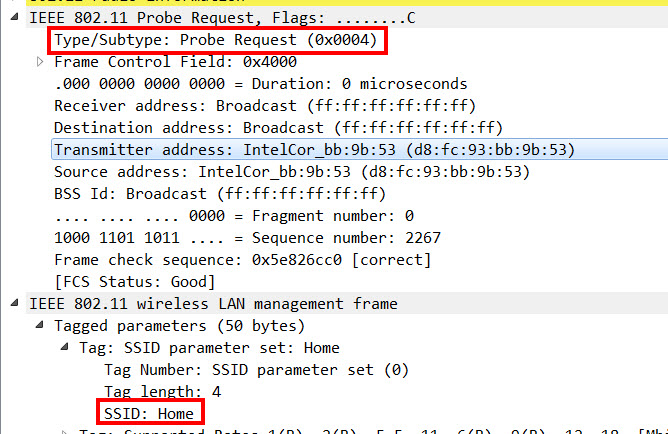
They define a “Wireless LAN Access Point” as a method that provides wireless access in public spaces or private areas to the internet, usually based on the IEEE-802.11-Standard.
When is a Wireless LAN “public”?
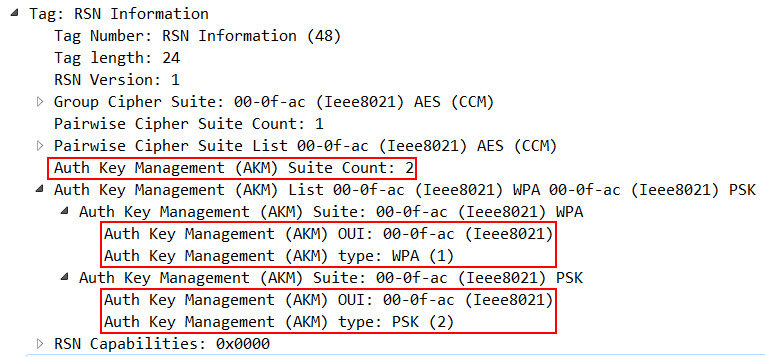
A Wirelss LAN is public, when it provides network access to third party, even if it is password protected. So a WPA/WPA2-Personal protected Wireless LAN does not suffice if the passcode is printed out hanging on the wall.
What defines “professionally maintained”?
A “Wireless LAN Access Point” is “professionally maintanied”, if it is maintained from an individual or a company that maintains multiple “Public Wireless LANs” on “multiple sites”.
Furthermore, they define “maintain” as providing one or more of the following services:
– configuration management
– remote or on site support
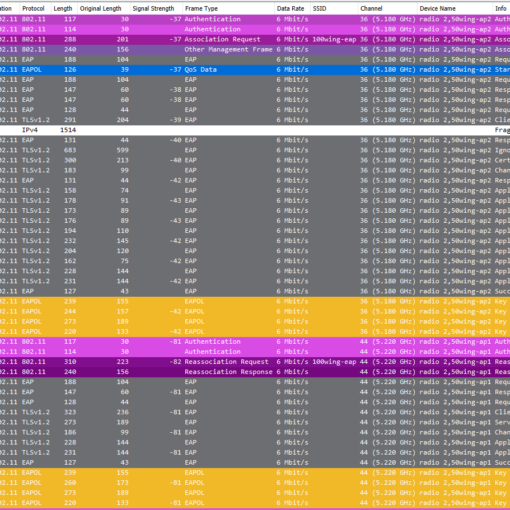
– access control, authorization management, AAA
– monitoring
– software- and firmware-updates
– capacity management
– end user support
What are “suitable methods” of identification?
As an example, the following methods for identification are presented:
– access code sent via SMS (storing of MSISDN)
– credit card
– trusted information from roaming-partner (WISPr, eduroam)
– individual access code per hotel room connected to a guest registration
– boarding card in airports
– frequent flyer program card
Personal opinion
I think, the intention itself is good – in cases where crimes are committed over the internet, they now have a way to identify the people behind it.
Unfortunately, it is not thought through and gives a false sense of security:
– If the criteria of “professionally maintained” is not met, you can do to your Wireless LAN whatever you want. You do not even have to protect it, and people who are up to no good can use it for their bad intentions. This new article punishes the people and companies that professionally provide Wireless LANs, but it is just not consistent.
– Identification of captive portals are usually based on MAC addresses. MAC spoofing is an easy way to piggyback someone elses connection. So basically, even if someone is convicted as the culprit, he can plead that it wasn’t him – and there is no way to be sure.
Cheers Renzo
Sources:
Merkblatt “WLAN”: https://www.li.admin.ch/sites/default/files/2018-02/Merkblatt%20WLAN.pdf
SR 780.11: https://www.admin.ch/opc/de/classified-compilation/20172173/index.html